Core Firewalling & Routing Defense
Perimeter and network connectivity form the foundation of secure operations for the entire organisation. This is where it's decided how the company protects infrastructure entry points, securely connects locations and withstands internet attacks and operational outages.
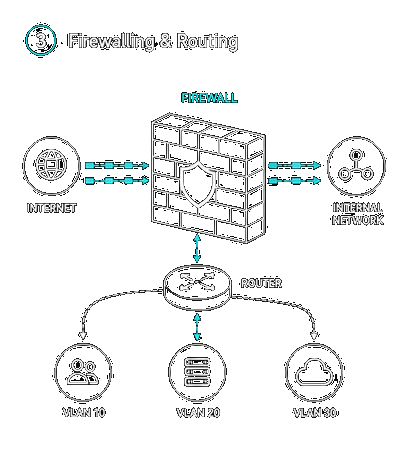
Perimeter protection by design
The perimeter is the first line of defence against external attacks and a key point for controlling access to the internal environment. We deploy firewalls, IDS/IPS, DDoS protection, secure DNS and other elements to stop threats as early as possible and keep network entry controlled.
But quality perimeter protection doesn't rest on technology alone. Equally important is correct rule configuration, segmentation, policy lifecycle review and eliminating weak points that companies often underestimate for years.
Auditable access and secure connectivity
A company needs visibility into who enters the environment, when and from where. We connect firewalls with access management, identity verification and traffic monitoring so that access can be audited, evaluated and continuously adjusted.
Secure hybrid connectivity is also a critical topic. Modern organisations operate across branches, data centres, suppliers, remote workers and cloud services. We design encrypted interconnections, secure remote access and standardised security policies across locations.
Application and service resilience
This area also covers protection against overload, outages and service availability disruption. DDoS protection, controlled access to applications and databases and stable routing infrastructure help maintain operations even under increased load or targeted attack.
The result is a stable and secure network foundation on which further security layers and future business development can be built.
Interested?
Let's set up a no-obligation consultation. We'll review your situation and suggest concrete steps.
Book a consultation